How to create AWS IAM Role using CloudFormation
This post explains how to create, update AWS IAM Role using CloudFormation and provides YAML and JSON example CloudFormation templates for creating IAM Instance Profiles, IAM Inline Policies and IAM Managed Policies.
See Also
- AWS cfn template for SQS queue
- AWS cfn template for Lambda function
- AWS cfn template for SNS topic and subscription
- AWS cfn templates for DynamoDB tables
Topics
- Create and Deploy IAM Role using YAML CFT
- Update existing IAM Role using YAML CFT
- Example CloudFormation YAML template to create Instance profile
- Example CloudFormation YAML template to embed inline policy to IAM role
- Example CloudFormation YAML template to create and attach managed policy to IAM role
- Example CloudFormation JSON template to create Instance profile
- Example CloudFormation JSON template to embed inline policy to IAM role
- Example CloudFormation JSON template to create and attach managed policy to IAM role
Creating and deploying IAM Role using YAML template
Let's create a IAM role to provide read access to S3 buckets. For providing
readonly access to IAM role we would be attaching
AmazonS3ReadOnlyAccess
managed policy to the role.
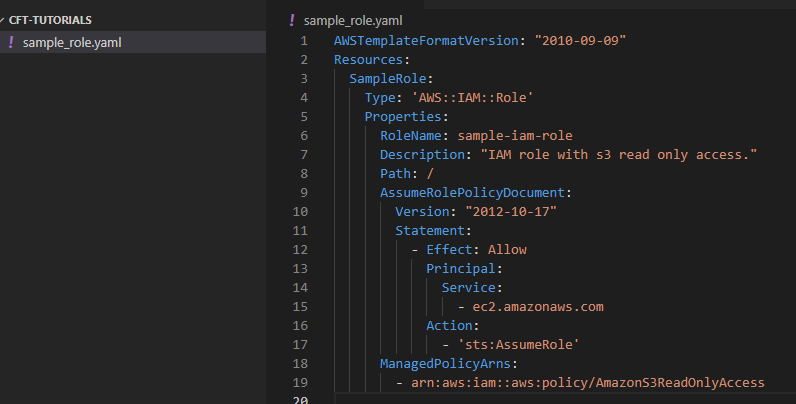
Step 1: Create directory with name cft-tutorials and open it in vscode.
Step 2: Create a file sample_role.yaml inside cft-tutorials.
Step 3: Copy the below YAML template in sample_role.yaml.
AWSTemplateFormatVersion: "2010-09-09"
Resources:
SampleRole:
Type: 'AWS::IAM::Role'
Properties:
RoleName: sample-iam-role
Description: "IAM role with s3 read only access."
Path: /
AssumeRolePolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: Allow
Principal:
Service:
- ec2.amazonaws.com
Action:
- 'sts:AssumeRole'
ManagedPolicyArns:
- arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess
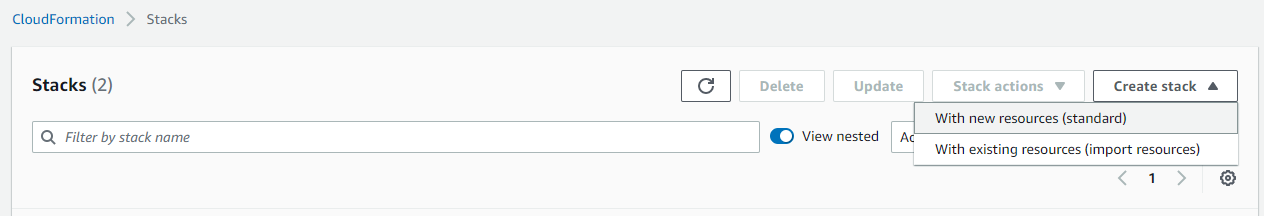
Step 4: Open the AWS CloudFormation directly with the URL https://console.aws.amazon.com/cloudformation/ .
Step 5: Navigate to Stacks, Click on Create stack and click on With new resources (standard).
Step 6: Select Template is ready . Select Upload a template file. Click on Choose file to select sample_role.yaml from cft-tutorials directory and click on Next.
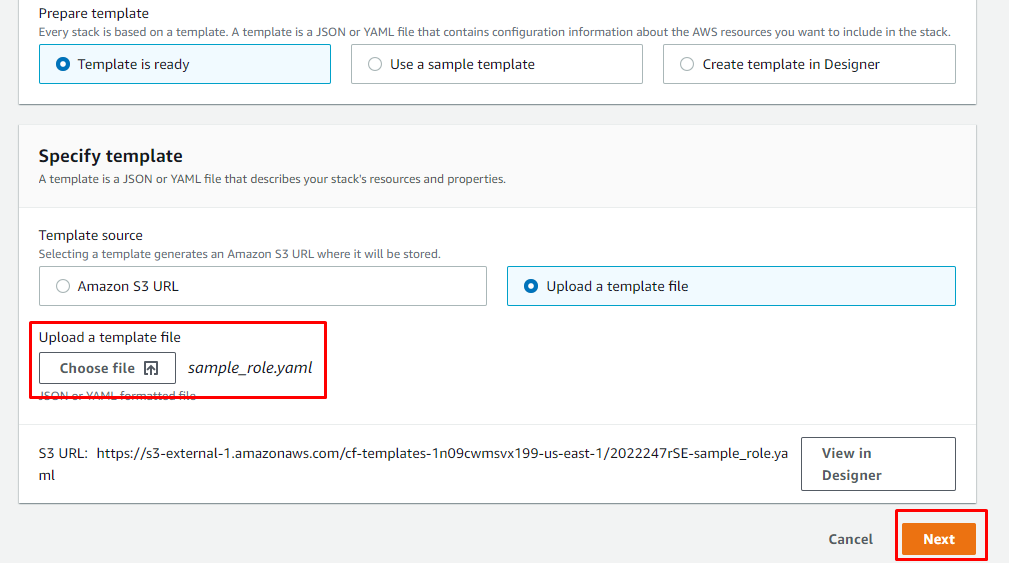
Step 7: Enter Stack name and click on Next.

Step 8: In "Configure stack options" page click on Next.
Step 9: Scroll down to check the confirmation for creating IAM roles and click on Create stack.
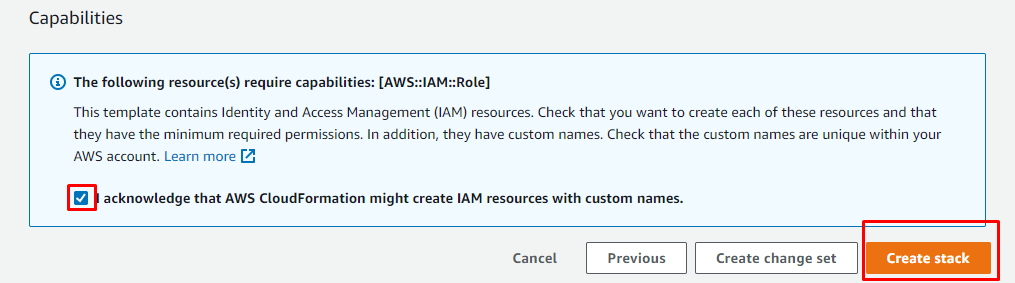
Step 10: Check Stack Events section, on completion you should see CREATE_COMPLETE for the stack.
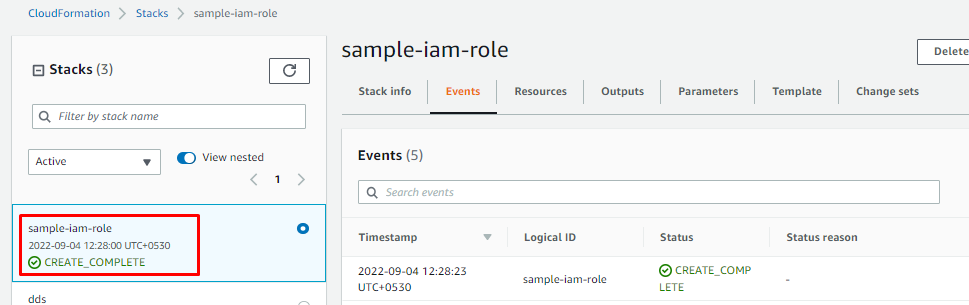
Now we have created an IAM role, lets update the role by adding tags using CloudFormation template.
Adding Tag to existing IAM Role using YAML template
Step 11: Update sample_role.yaml with below template.
AWSTemplateFormatVersion: "2010-09-09"
Resources:
SampleRole:
Type: 'AWS::IAM::Role'
Properties:
RoleName: sample-iam-role
Description: "IAM role with s3 read only access."
Path: /
AssumeRolePolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: Allow
Principal:
Service:
- ec2.amazonaws.com
Action:
- 'sts:AssumeRole'
ManagedPolicyArns:
- arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess
Tags:
- Key: "Name"
Value: "Sample Role"
- Key: "Purpose"
Value: "Tutorial"
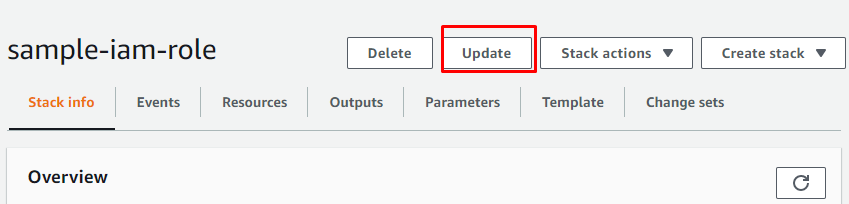
Step 12: Navigate to stack created in Step 9 and click on Update.
Step 13: Select Replace current template . Select Upload a template file. Click on Choose file to select sample_role.yaml from cft-tutorials directory and click on Next.

Step 14: In "Stack details" and "Configure stack options" pages click on Next.
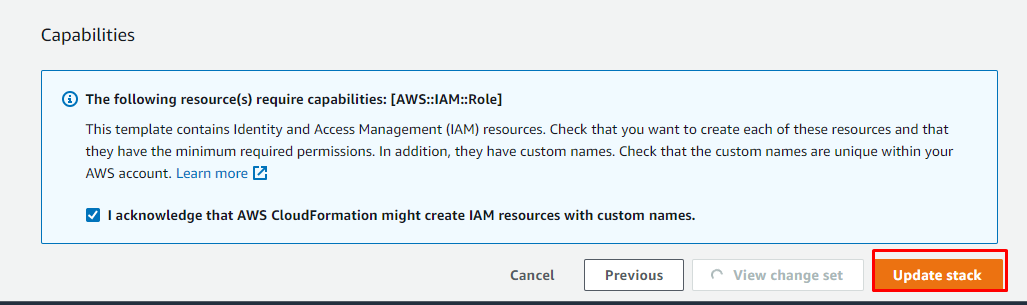
Step 15: Scroll down to check the confirmation for creating IAM roles and click on Update stack.
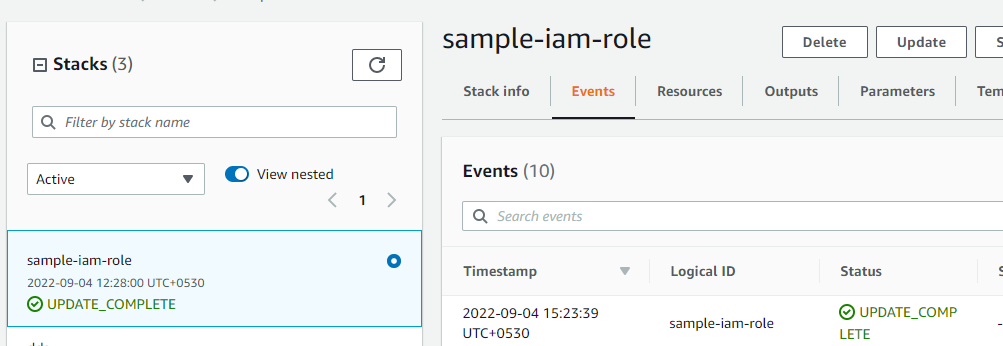
Step 16: Check Stack Events section, on completion you should see UPDATE_COMPLETE for the stack.
IAM Role YAML CloudFormation Template Examples
Below are the some the common IAM role CloudFormation templates examples for use cases like creating instance profile, attaching an external policy etc.
IAM Role YAML template for creating instance profile
Following YAML CloudFormation template creates an IAM Role and an instance profile to pass an IAM role to an EC2 instance.
AWSTemplateFormatVersion: "2010-09-09"
Resources:
SampleRole:
Type: 'AWS::IAM::Role'
Properties:
RoleName: sample-iam-role
Description: "IAM role with s3 read only access."
Path: /
AssumeRolePolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: Allow
Principal:
Service:
- ec2.amazonaws.com
Action:
- 'sts:AssumeRole'
ManagedPolicyArns:
- arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess
Tags:
- Key: "Name"
Value: "Sample Role"
- Key: "Purpose"
Value: "Tutorial"
# Create Instance Profile
SampleRoleInstanceProfile:
Type: "AWS::IAM::InstanceProfile"
Properties:
Path: "/"
Roles:
- Ref: "SampleRole"
YAML template for embedding IAM inline Policy to IAM Role
CFT template shown below creates an IAM role and embeds Inline policy to IAM role.
AWSTemplateFormatVersion: "2010-09-09"
Resources:
# IAM Role
SampleRole:
Type: 'AWS::IAM::Role'
Properties:
RoleName: sample-iam-role
Description: "IAM role with s3 read only access."
Path: /
AssumeRolePolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: Allow
Principal:
Service:
- ec2.amazonaws.com
Action:
- 'sts:AssumeRole'
ManagedPolicyArns:
- arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess
Tags:
- Key: "Name"
Value: "Sample Role"
- Key: "Purpose"
Value: "Tutorial"
# Attach inline policy to IAM Role
RolePolicies:
Type: "AWS::IAM::Policy"
Properties:
PolicyName: "sampleRolePolicy"
PolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: "Allow"
Action: ec2:Describe
Resource: "*"
Roles:
- Ref: "SampleRole"
YAML template for creating and attaching Managed IAM Policy to IAM Role
Below CloudFormation templates creates an IAM Role, embeds Inline policy to IAM role and creates and attaches manged policy to IAM Role.
AWSTemplateFormatVersion: "2010-09-09"
Resources:
# IAM Role
SampleRole:
Type: 'AWS::IAM::Role'
Properties:
RoleName: sample-iam-role
Description: "IAM role with s3 read only access."
Path: /
AssumeRolePolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: Allow
Principal:
Service:
- ec2.amazonaws.com
Action:
- 'sts:AssumeRole'
ManagedPolicyArns:
- arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess
Tags:
- Key: "Name"
Value: "Sample Role"
- Key: "Purpose"
Value: "Tutorial"
# Attach inline policy to IAM Role
RolePolicies:
Type: "AWS::IAM::Policy"
Properties:
PolicyName: "sampleRolePolicy"
PolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: "Allow"
Action: ec2:Describe
Resource: "*"
Roles:
- Ref: "SampleRole"
# Create managed policy and attach to IAM Role
ManagedRolePolicy:
Type: "AWS::IAM::ManagedPolicy"
Properties:
ManagedPolicyName: "sampleManagedPolicy"
PolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: "Allow"
Action:
- ec2:CreateTags
- ec2:DeleteTags
Resource: "*"
Roles:
- Ref: "SampleRole"
JSON IAM Role CloudFormation Template Examples
Below are the some the common IAM role JSON CloudFormation templates examples for use cases like creating instance profile, attaching an external policy etc.
IAM Role JSON template for creating instance profile
Following JSON CloudFormation template creates an IAM Role and an instance profile to pass an IAM role to an EC2 instance.
{
"AWSTemplateFormatVersion": "2010-09-09",
"Resources": {
"SampleRole": {
"Type": "AWS::IAM::Role",
"Properties": {
"RoleName": "sample-iam-role",
"Description": "IAM role with s3 read only access.",
"AssumeRolePolicyDocument": {
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Service": ["ec2.amazonaws.com"]
},
"Action": ["sts:AssumeRole"]
}
]
},
"Path": "/",
"ManagedPolicyArns": ["arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess"],
"Tags": [
{
"Key": "Name",
"Value": "Sample Role"
},
{
"Key": "Purpose",
"Value": "Tutorial"
}
]
}
},
"SampleRoleInstanceProfile": {
"Type": "AWS::IAM::InstanceProfile",
"Properties": {
"Path": "/",
"Roles": [
{
"Ref": "SampleRole"
}
]
}
}
}
}
JSON template for embedding IAM inline Policy to IAM Role
JSON CFT template shown below creates an IAM role and embeds Inline policy to IAM role.
{
"AWSTemplateFormatVersion": "2010-09-09",
"Resources": {
"SampleRole": {
"Type": "AWS::IAM::Role",
"Properties": {
"RoleName": "sample-iam-role",
"Description": "Sample IAM role",
"AssumeRolePolicyDocument": {
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Service": ["ec2.amazonaws.com"]
},
"Action": ["sts:AssumeRole"]
}
]
},
"Path": "/",
"ManagedPolicyArns": ["arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess"],
"Tags": [
{
"Key": "Name",
"Value": "Sample Role"
},
{
"Key": "Purpose",
"Value": "Tutorial"
}
]
}
},
"InlineRolePolicies": {
"Type": "AWS::IAM::Policy",
"Properties": {
"PolicyName": "root",
"PolicyDocument": {
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "ec2:Describe",
"Resource": "*"
}
]
},
"Roles": [
{
"Ref": "SampleRole"
}
]
}
}
}
}
JSON CFT template for creating and attaching Managed IAM Policy to IAM Role
Below JSON CloudFormation templates creates an IAM Role, embeds Inline policy to IAM role and creates and attaches manged policy to IAM Role.
{
"AWSTemplateFormatVersion": "2010-09-09",
"Resources": {
"SampleRole": {
"Type": "AWS::IAM::Role",
"Properties": {
"RoleName": "sample-iam-role",
"Description": "Sample IAM Role",
"AssumeRolePolicyDocument": {
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Service": ["ec2.amazonaws.com"]
},
"Action": ["sts:AssumeRole"]
}
]
},
"Path": "/",
"ManagedPolicyArns": ["arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess"],
"Tags": [
{
"Key": "Name",
"Value": "Sample Role"
},
{
"Key": "Purpose",
"Value": "Tutorial"
}
]
}
},
"SampleRoleManagedPolicy": {
"Type": "AWS::IAM::ManagedPolicy",
"Properties": {
"Description": "Sample role managed policy",
"Path": "/",
"PolicyDocument": {
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": ["ec2:CreateTags", "ec2:DeleteTags"],
"Resource": "*"
}
]
},
"Roles": [
{
"Ref": "SampleRole"
}
]
}
}
}
}
Category: AWS
